

This project documents the design and implementation of a cloud-native detection pipeline in AWS. The goal was to simulate sensitive API activity, detect it in near real-time, and store structured alert data for analysis. Rather than simply provisioning resources, this lab demonstrates how activity inside an AWS account can be monitored, detected, and preserved for investigation.
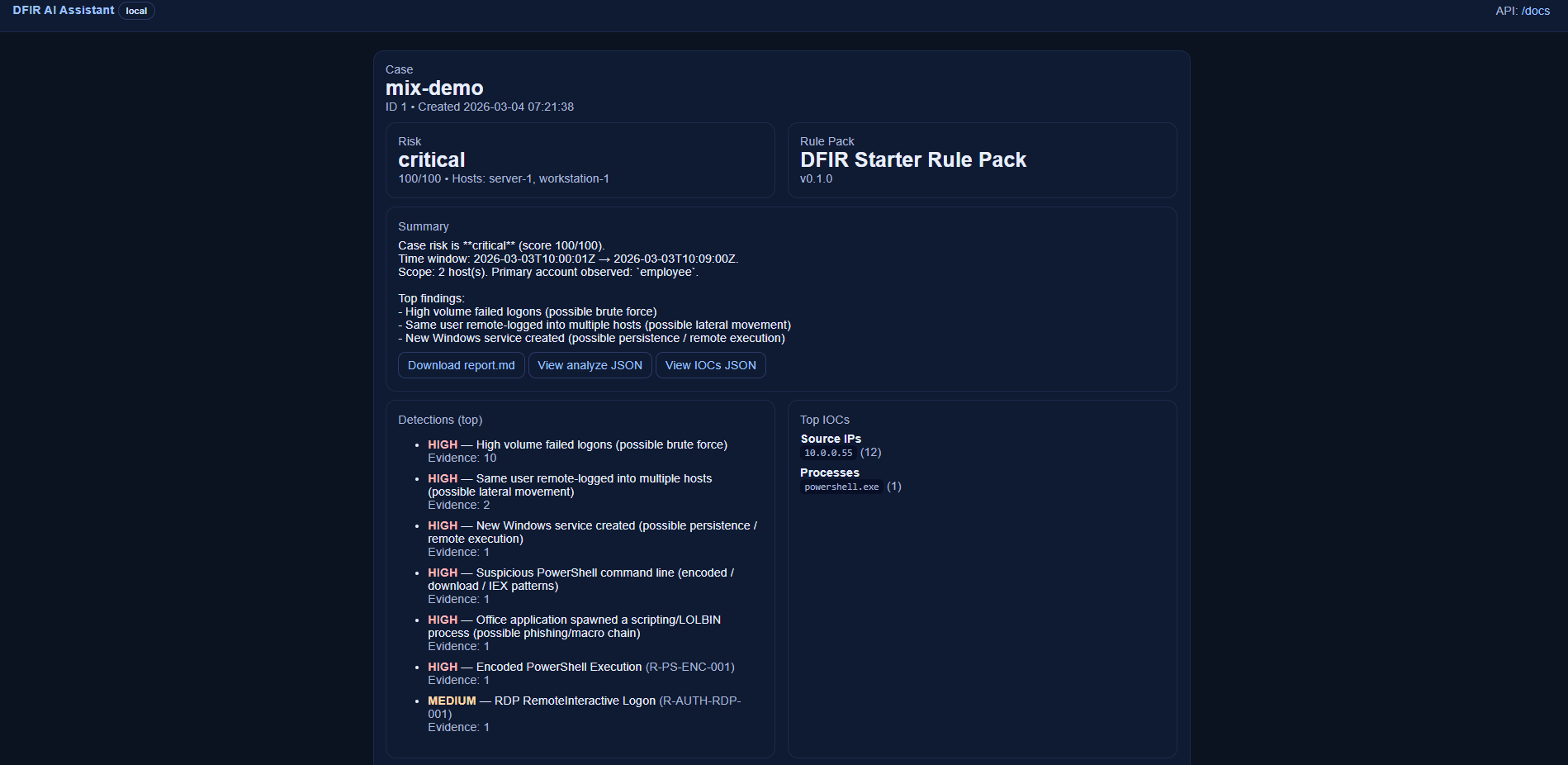
The DFIR AI Assistant is a security investigation tool I built to automate parts of the digital forensics and incident response workflow. It ingests Windows event logs, detects suspicious activity such as brute force attempts, encoded PowerShell execution, and possible lateral movement, then generates a structured case report with a timeline of events and key indicators of compromise. A SOC-style dashboard allows analysts to review cases and investigate findings.
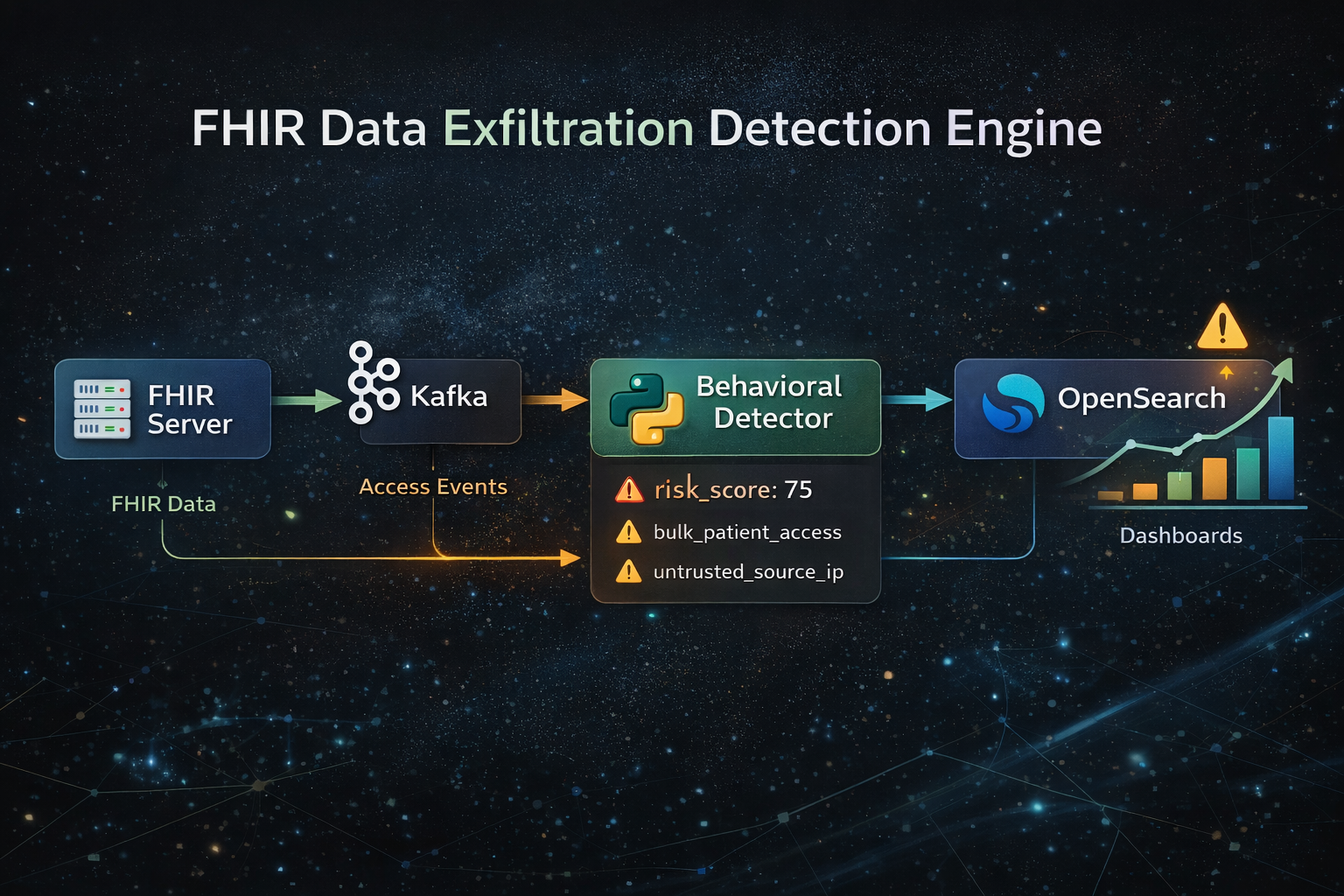
This project is a healthcare-focused detection engine designed to identify abnormal access patterns in FHIR-based patient data systems. Instead of relying on traditional infrastructure-level security signals, it analyzes how data is accessed over time to detect behaviors such as bulk data scraping, off-hours activity, and misuse of service accounts. The system simulates realistic FHIR API interactions, streams access events through Kafka, and applies deterministic, explainable risk scoring using Python. Enriched events are then indexed into OpenSearch, where they can be visualized and investigated through dashboards. By focusing on behavioral analytics and explainability, this project demonstrates how real-world detection engineering can be applied to protect sensitive healthcare data from insider threats and credential misuse.
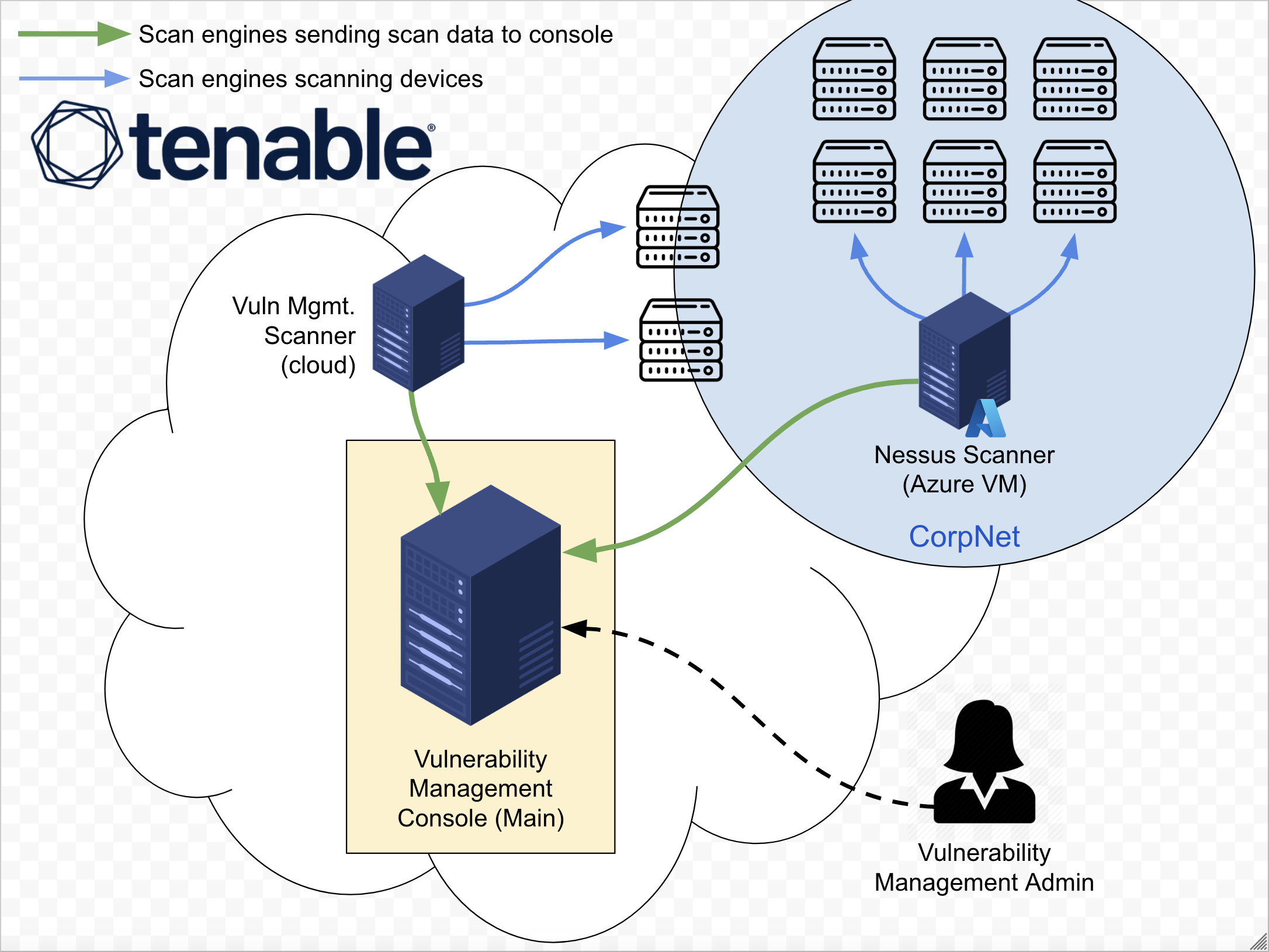
In this project, I simulate the implementation of a comprehensive vulnerability management program, from inception to completion. Inception State: the organization has no existing policy or vulnerability management practices in place. Completion State: a formal policy is enacted, stakeholder buy-in is secured, and a full cycle of organization-wide vulnerability remediation is successfully completed.